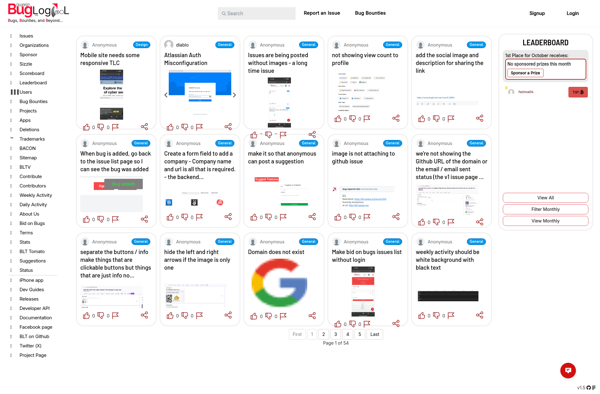
Description: Bugheist is a bug bounty platform that allows developers to incentivize ethical hackers to find security vulnerabilities in their software. It connects businesses with security researchers in a crowdsourced model to improve code security.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
Description: SafeHats Bug Bounty is an ethical hacking platform that allows security researchers to responsibly disclose vulnerabilities in SafeHats web assets. It rewards researchers for finding bugs.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API