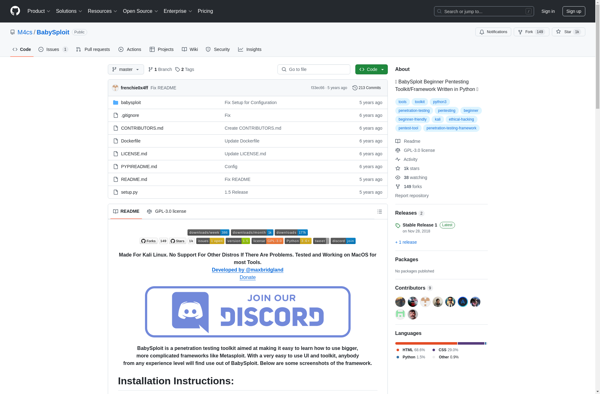
Description: BabySploit is an open-source penetration testing toolkit designed for beginners to learn about ethical hacking and cybersecurity. It provides a simple interface and various basic hacking tools to test network vulnerabilities without advanced knowledge.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
Description: Cobalt Strike is a commercial penetration testing tool used to simulate adversarial attacks against networks. It helps testers find vulnerabilities and gain access similar to real-world threats.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API