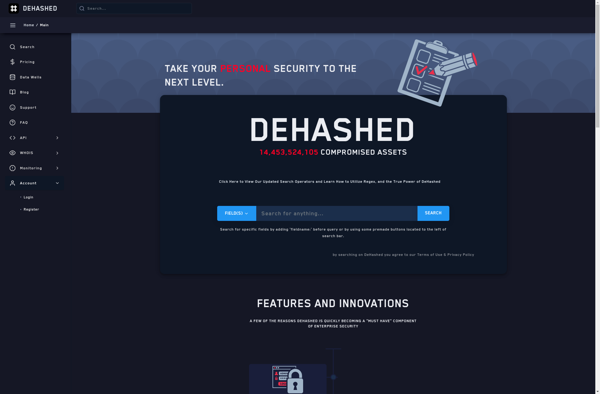
Description: DeHashed is an OSINT tool for searching emails, usernames, passwords, domains, IP addresses, and phone numbers that have been leaked in data breaches. It allows users to check if their information has been exposed online.
Type: software
Description: LeakCorp is a software tool that helps companies identify and prevent data leaks. It monitors employee communications and activity to flag potential threats and policy violations. The software uses AI to analyze trends and patterns that suggest risk.
Type: software