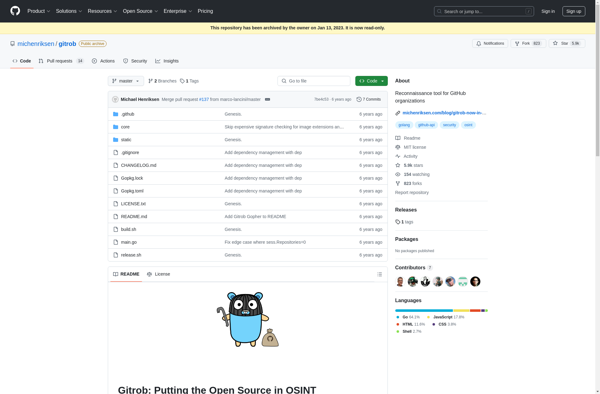
Description: Gitrob is an open source reconnaissance tool used to find potentially sensitive files and information exposed in GitHub repositories. It helps security researchers and pentesters identify misconfigured GitHub repos that leak API keys, passwords, PII, and other sensitive data.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
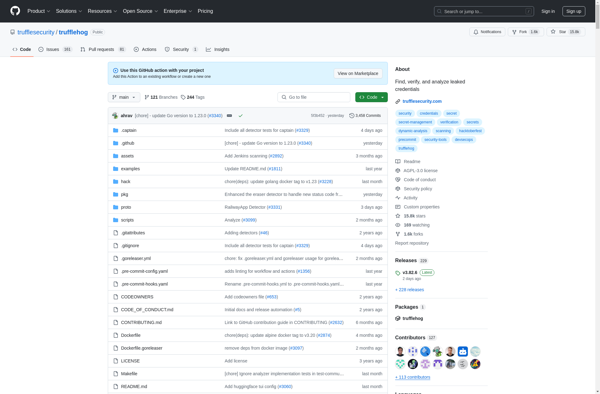
Description: TruffleHog is an open source tool for finding secrets and passwords that have been committed to git repositories. It scans git histories for high entropy strings and secrets, letting developers and security teams find and revoke credentials that have been accidentally committed.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API