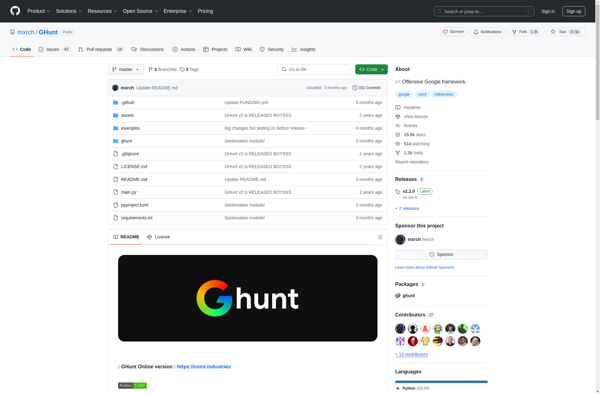
Description: GHunt is an open source OSINT tool used to find usernames across multiple social networks based on search strings and data breaches. It helps aggregate information about identity exposure risks.
Type: software
Pricing: Open Source
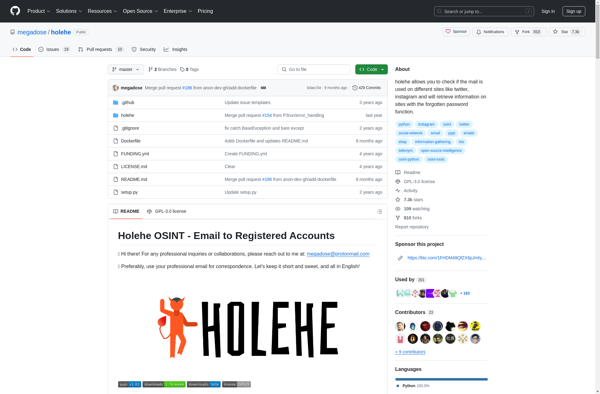
Description: Holehe is an open source tool used to check if email addresses have been compromised in data breaches. It searches through publicly available data breach databases to see if the entered email address appears exposed in any breaches.
Type: software
Pricing: Open Source