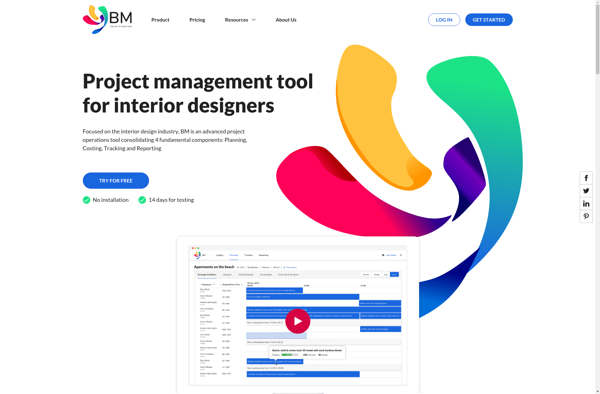
Description: Binary Management is software that helps organizations manage and secure their binary code assets. It provides capabilities like cataloging binaries, tracking their provenance, identifying security issues, controlling distribution, and automating policy enforcement.
Type: software
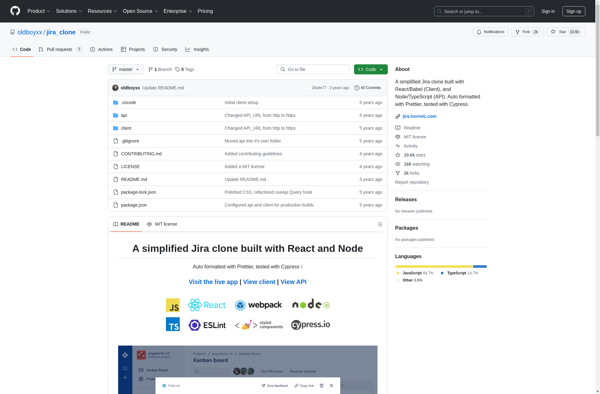
Description: A Jira clone is project management software that mimics the core functionalities of Atlassian's Jira product. It provides tools for agile development teams to plan, track, and release software projects.
Type: software
Pricing: Open Source