Description: Load Tester is a performance and load testing software used to simulate user traffic against web and mobile applications to identify bottlenecks. It helps test application stability under various realistic load conditions.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
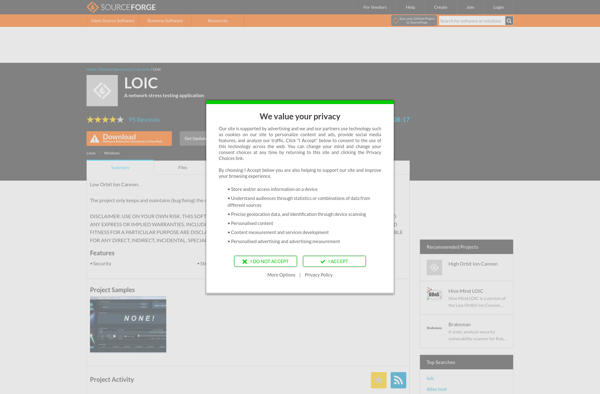
Description: Low Orbit Ion Cannon (LOIC) is an open-source network stress testing and denial-of-service attack application. It allows users to flood a target server with TCP, UDP, or HTTP requests to try to overwhelm and take down the target.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API