Description: Enzoic is a password security platform that helps prevent data breaches by protecting against weak, reused, and compromised passwords. It integrates with existing systems to analyze password risk in real-time and take automated actions like requiring password changes or multi-factor authentication.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
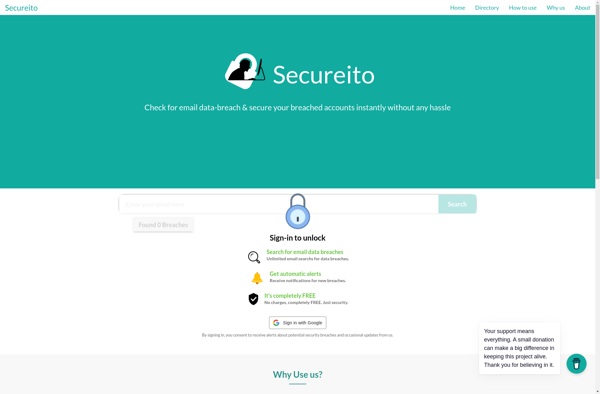
Description: Secureito is a data security and governance platform that helps organizations discover, classify, and protect sensitive data across cloud and on-premises environments. It uses AI and machine learning for automatic data discovery and classification.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API