Description: OpenVPN is an open-source software application that implements virtual private network (VPN) techniques for creating secure point-to-point or site-to-site connections in routed or bridged configurations and remote access facilities. It uses a custom security protocol that utilizes SSL/TLS for key exchange. It is capable of traversing network address translation (NAT) and firewalls.
Type: software
Pricing: Free
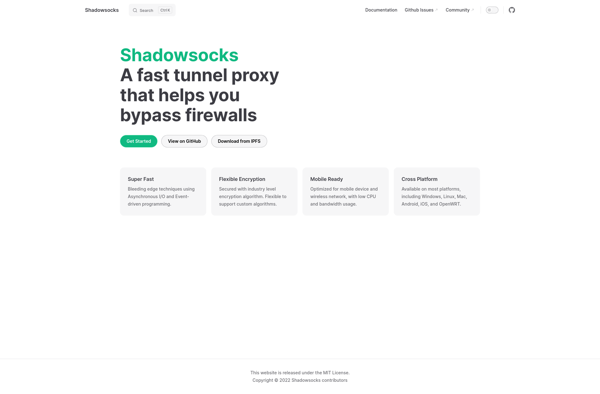
Description: Shadowsocks is an open-source, cross-platform web proxy tool that helps users bypass firewalls and access restricted websites. It works by creating an encrypted connection between the client and server to secure and encrypt internet traffic.
Type: software
Pricing: Open Source