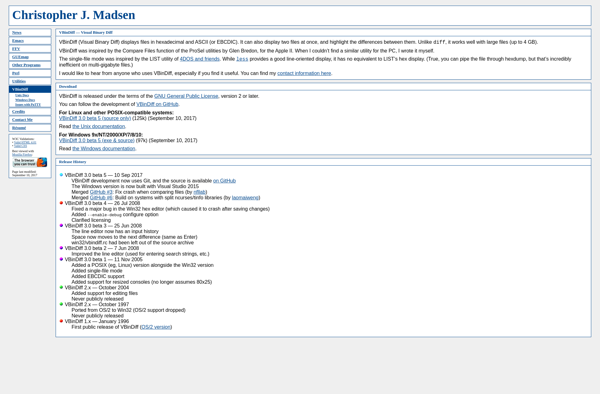
Description: VBinDiff is a binary code comparison tool used for malware analysis, vulnerability research, and reverse engineering. It quickly compares binary executables and libraries to identify similarities, differences, new features, bugs, security flaws, and more.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
Description: wxHexEditor is an open source hex editor for Windows, Linux and macOS. It allows users to view, edit and analyze binary files in hexadecimal format. Common uses include editing program files, reverse engineering binaries, analyzing network packets and disk forensics.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API