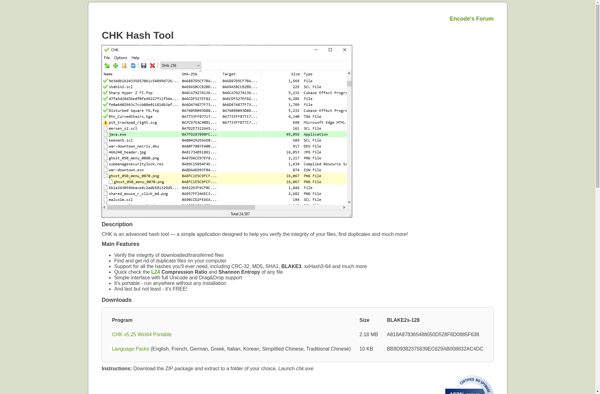
Description: CHK Checksum Utility is a free software utility that calculates and verifies checksums to validate file integrity and detect data corruption. It supports a wide range of hashing and checksum algorithms.
Type: software
Pricing: Open Source
Description: DeadHash is an open-source password cracking tool for Windows, Linux and macOS. It supports CPU and GPU hardware acceleration for cracking passwords up to 64 characters long through hashcat.
Type: software
Pricing: Open Source