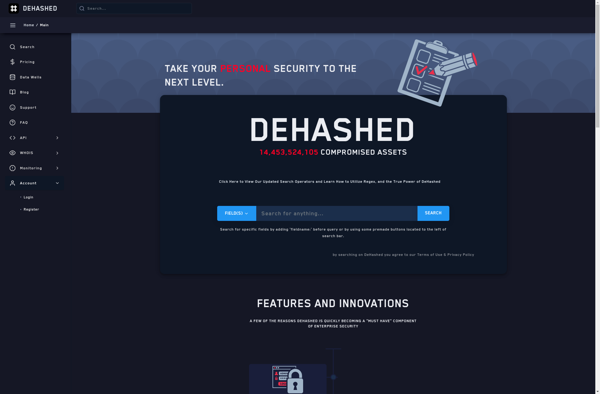
Description: DeHashed is an OSINT tool for searching emails, usernames, passwords, domains, IP addresses, and phone numbers that have been leaked in data breaches. It allows users to check if their information has been exposed online.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
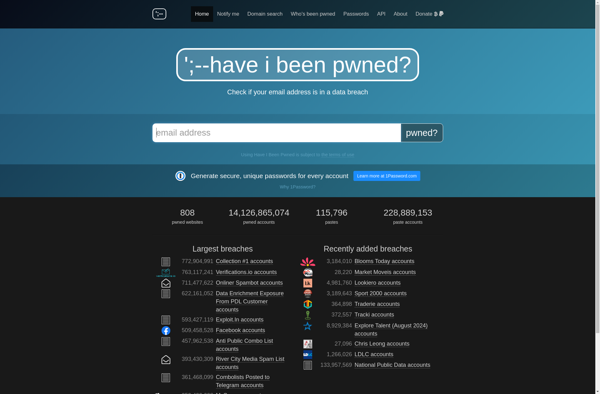
Description: Have I been pwned? is a website that allows internet users to check if their personal data has been compromised by data breaches. It contains a database of breached accounts and allows users to search to see if their email address or phone number appears.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API