Description: Armitage is a graphical cyber attack management tool for Metasploit that helps automate exploit and payload selection. It streamlines attacking multiple hosts and allows the use of exploits in metasploit via a graphical user interface instead of command line.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
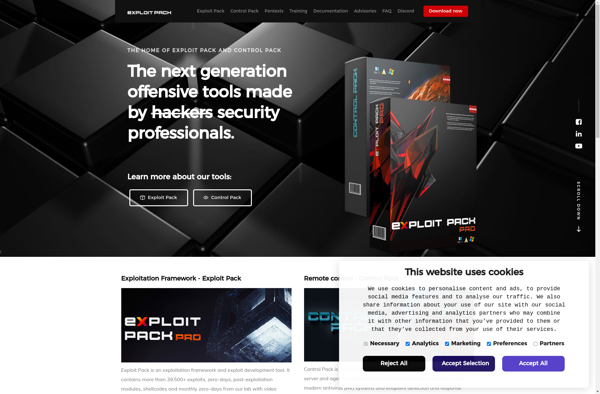
Description: Exploit Pack is a penetration testing tool used to simulate cyber attacks and exploit vulnerabilities in order to evaluate the security of networks and applications. It contains a collection of exploits and payloads to mimic real-world hacking scenarios.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API