Description: DeadHash is an open-source password cracking tool for Windows, Linux and macOS. It supports CPU and GPU hardware acceleration for cracking passwords up to 64 characters long through hashcat.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
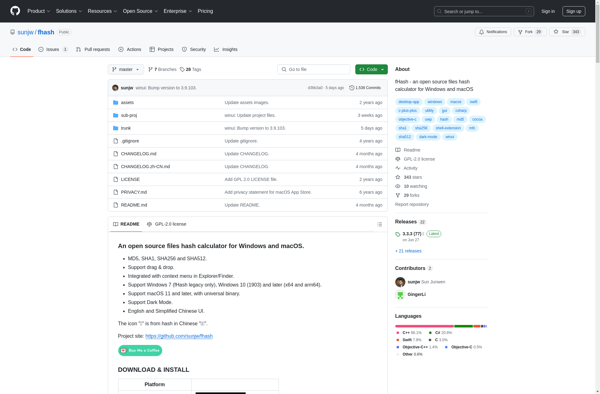
Description: fHash is an open source program used to identify similar or duplicate files on Windows systems. It analyzes and compares file content to detect duplicates, providing a GUI and CLI.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API