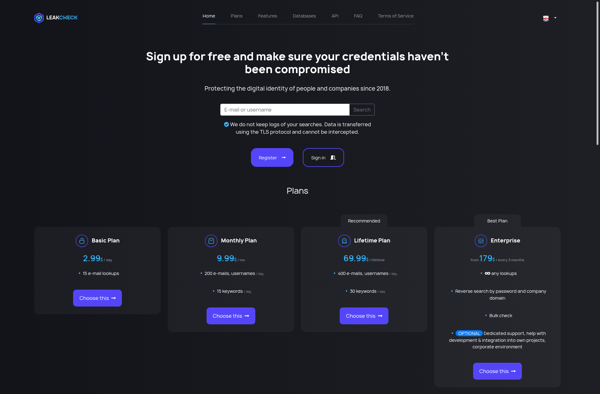
Description: Hacked Leaks Checker is a website that allows you to check if your email address or phone number has been compromised in a data breach. It searches through databases of leaked information and notifies you if your personal data is exposed.
Type: software
Pricing: Freemium
Description: LeakCheck is a free open-source memory leak detector for C and C++ programs. It helps developers identify memory leaks during development to avoid issues down the line. Easy to integrate and provides detailed leak reports.
Type: software
Pricing: Open Source