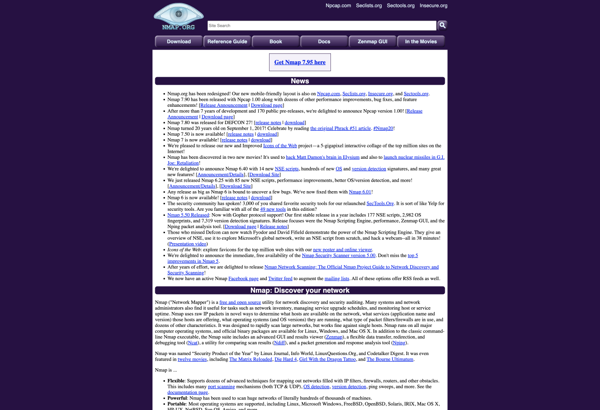
Description: Nmap is an open source network discovery and security auditing tool. It is used to discover hosts and services on a network and to detect potential vulnerabilities.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
Description: Nsauditor is a network security auditing and vulnerability assessment tool that scans networks to detect security issues. It checks for misconfigurations, known vulnerabilities, and open ports across devices. The tool is designed for IT administrators and security professionals.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API