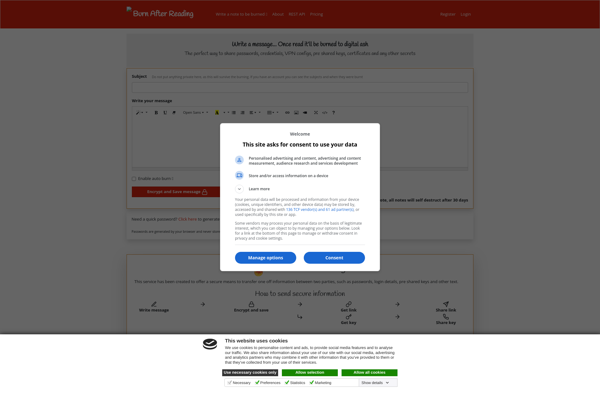
Description: Burn After Reading is a secure file deletion software that permanently deletes files so they cannot be recovered. It allows securely removing sensitive files from hard drives.
Type: software
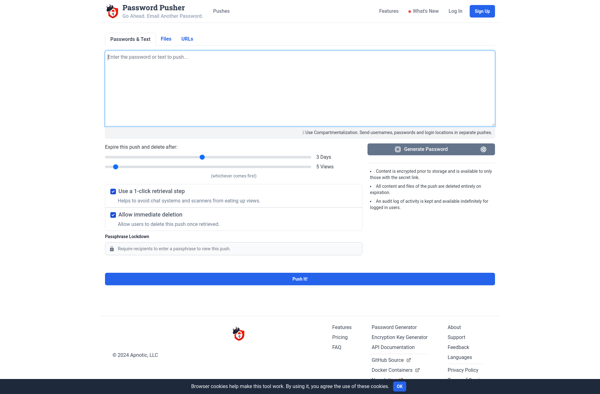
Description: Password Pusher is a self-hosted password management solution that allows individuals and teams to securely store passwords. It has features like password generation, sharing, automatic logins, and more.
Type: software
Pricing: Open Source