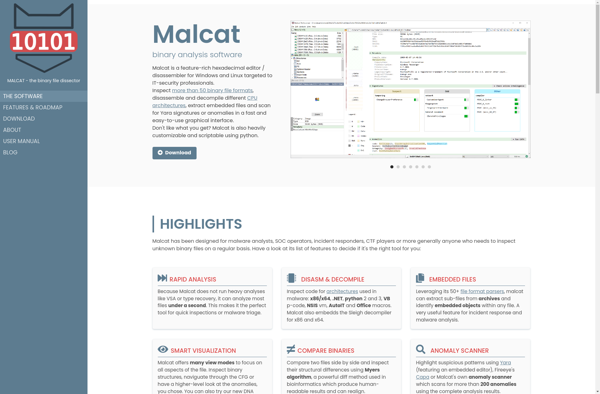
Description: Malcat is an open-source malware analysis tool that allows users to analyze malicious files, extract payloads, perform static analysis, and gather threat intelligence. It has support for a wide variety of file types including PE files, scripts, documents, and memory dumps.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
Description: PE-bear is a free, open source portable executable (PE) malware analysis tool. It performs static analysis on Windows executable files to extract metadata and identify suspicious characteristics.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API