Description: Bearer is a password manager and digital vault app that allows users to securely store passwords, sensitive documents, photos, videos, and other files. It uses AES-256 bit encryption to protect user data.
Type: software
Pricing: Freemium
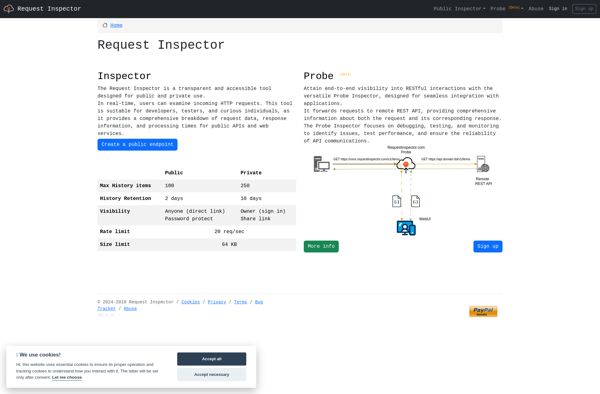
Description: Request Inspector is an open-source web debugging proxy software that allows developers to inspect HTTP requests and responses. It can be used to debug APIs, test performance, mock responses, and more.
Type: software
Pricing: Open Source