Description: Device Info is a lightweight utility that provides detailed information about the hardware components and configuration of your computer. It shows info about the CPU, motherboard, memory, drives, graphics card, operating system, and more.
Type: software
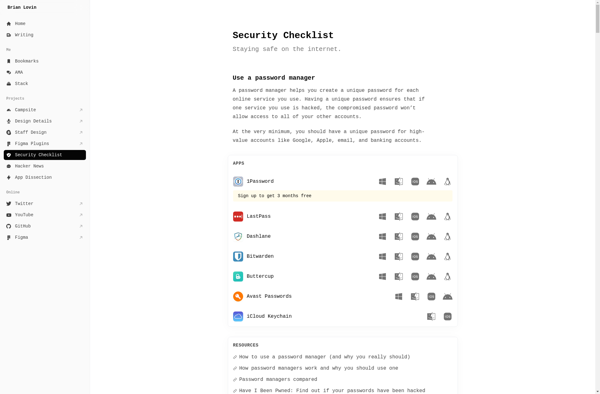
Description: Security Checklist is a software tool that allows users to create customized checklists for securing computers, servers, networks, and other IT infrastructure. It provides templates and guides for implementing security best practices.
Type: software