Description: Cyber Leader is an AI-powered cybersecurity software that provides real-time threat detection, response and remediation across IT infrastructures. It uses advanced behavioral analysis and machine learning to identify malicious activity and automate containment.
Type: software
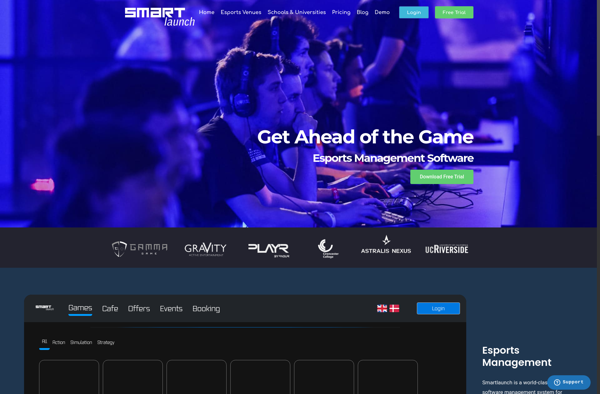
Description: Smartlaunch is a user-friendly software for building no-code internal business web applications quickly. It allows users to build customizable forms, workflows, reports and dashboards through an intuitive drag-and-drop interface.
Type: software