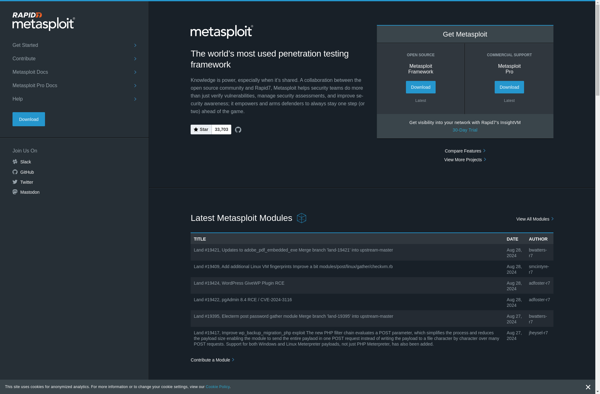
Description: Metasploit is an open source penetration testing framework that helps security professionals find, exploit, and validate vulnerabilities. It includes a database of known exploits and payloads that can be used to simulate attacks against systems to test their security.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
Description: The Social-Engineer Toolkit is an open-source penetration testing framework designed for social engineering attacks. It includes a variety of custom attack vectors that enable red teams and security researchers to simulate phishing, vishing, SMSishing and USB autorun attacks.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API