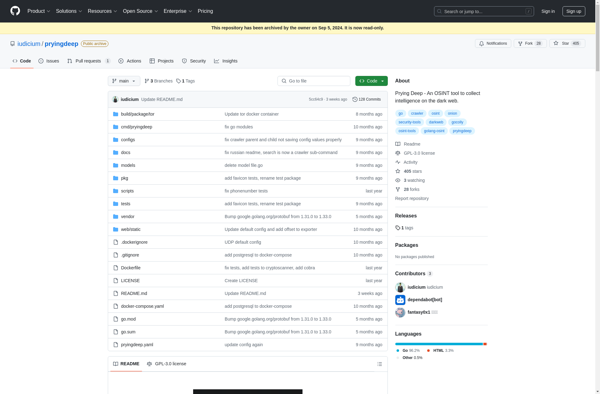
Description: Prying Deep is an open-source forensic analysis tool for inspecting Android applications. It can be used to analyze apps for malicious behavior or privacy concerns, as well as to reverse engineer the inner workings of apps. In 60 words or less, Prying Deep enables security analysts and Android developers to statically analyze Android APKs to understand how they work under the hood.
Type: software
Pricing: Open Source
Description: SpiderFoot is an open source intelligence (OSINT) automation tool used for gathering information from public sources. It helps collect data about IP addresses, domains, e-mail addresses, names, affiliations and more.
Type: software
Pricing: Open Source