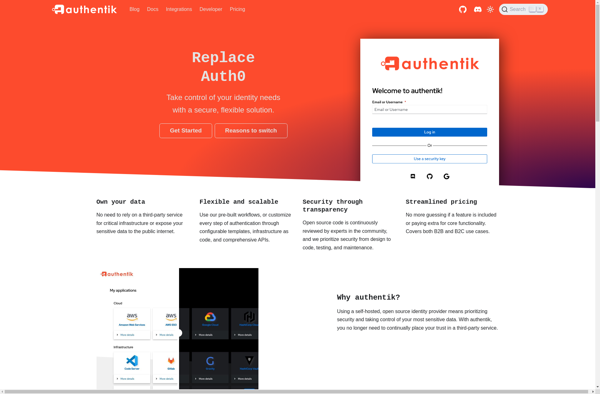
Description: authentik is an open-source identity provider and access management system. It allows centralized authentication and authorization for web applications and services. authentik is self-hosted, customizable, and integrates with Linux systems.
Type: software
Pricing: Open Source
Description: Stormpath is an API-first developer authentication and user management platform. It allows developers to easily add user authentication, authorization, social login, and security features to web and mobile applications. The service handles user storage, authentication flows, access control, and more out of the box.
Type: software