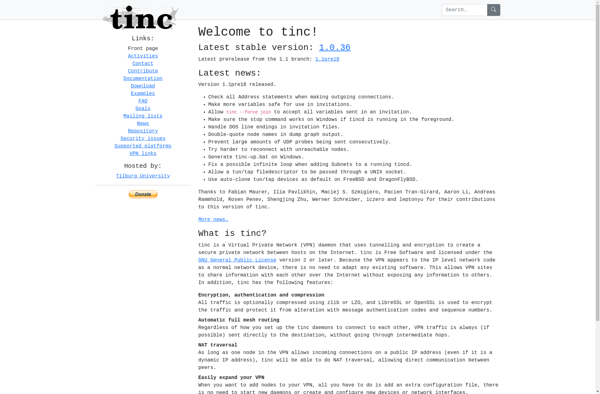
Description: Tinc VPN is an open-source, decentralized virtual private network (VPN) software that allows users to create a secure private network between devices and servers over the public internet. It uses encryption and authentication algorithms to establish secure tunnels without routing traffic through a central VPN server.
Type: software
Pricing: Open Source
Description: Twingate is a software-defined perimeter solution used to secure access to internal applications and resources. It sets up secure connections between users, devices, and applications without using VPNs.
Type: software