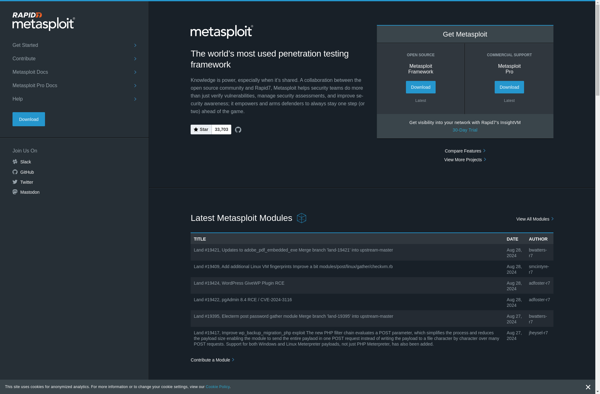
Description: Metasploit is an open source penetration testing framework that helps security professionals find, exploit, and validate vulnerabilities. It includes a database of known exploits and payloads that can be used to simulate attacks against systems to test their security.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
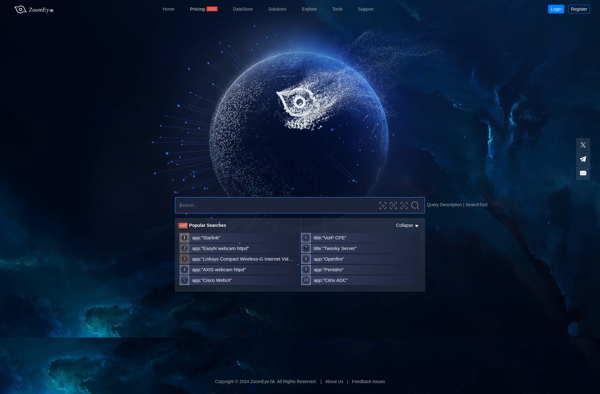
Description: ZoomEye is a search engine and data mining tool for cyberspace that facilitates the discovery and analysis of devices exposed to the public internet. It allows users to search for open ports, identify software and their versions, and uncover security risks.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API