Description: Cyberarms Intrusion Detection and Defense is a network security software that provides real-time monitoring to detect malicious activity and attacks. It uses behavioral analysis and machine learning to identify threats.
Type: software
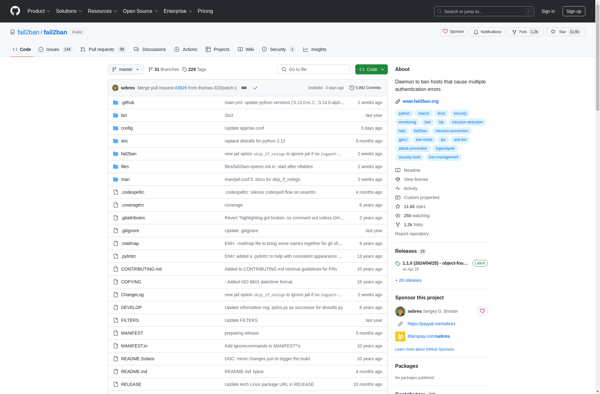
Description: Fail2ban is an open source intrusion prevention software framework that protects computer servers from brute-force attacks by banning IP addresses that attempt too many login failures.
Type: software
Pricing: Open Source