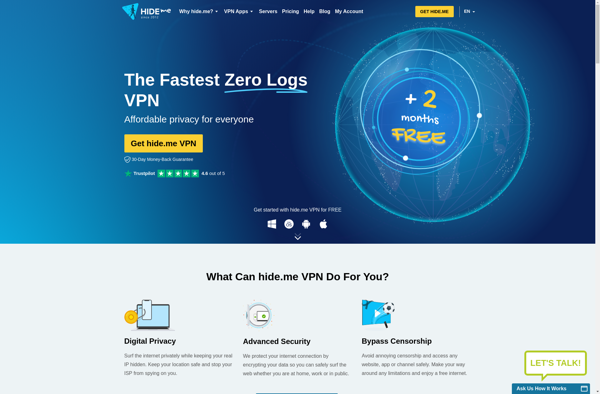
Description: Hide.me is a VPN service that allows users to browse the internet anonymously and securely. It offers strong encryption, no-logs policy, and servers in over 75 locations to help protect users' privacy online.
Type: software
Description: I2P is an anonymous network layer that allows applications to send messages to each other pseudonymously and securely. It is an overlay network that uses cryptography and tunnels to hide the identity and location of users.
Type: software
Pricing: Open Source