Description: i2pd is an open-source C++ implementation of the I2P anonymous network. It is designed to be a lightweight, fast, and secure way to access I2P services and route anonymous traffic.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
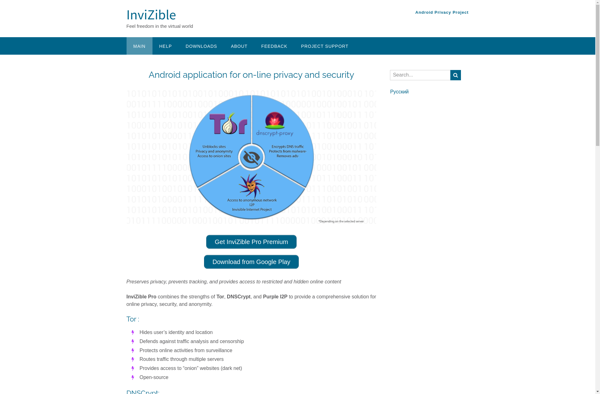
Description: InviZible Pro is a VPN service that provides encrypted connections to protect your privacy and security when browsing the internet. It has servers in over 50 countries, allows P2P traffic, and has apps for all major platforms.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API