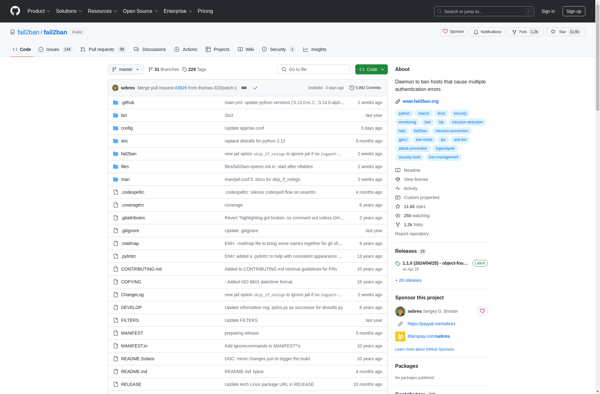
Description: Fail2ban is an open source intrusion prevention software framework that protects computer servers from brute-force attacks by banning IP addresses that attempt too many login failures.
Type: software
Pricing: Open Source
Description: LF Intrusion Detection is an open source intrusion detection system for Linux servers. It monitors network traffic and system logs for suspicious activity and alerts administrators when potential attacks or policy violations are detected.
Type: software
Pricing: Open Source