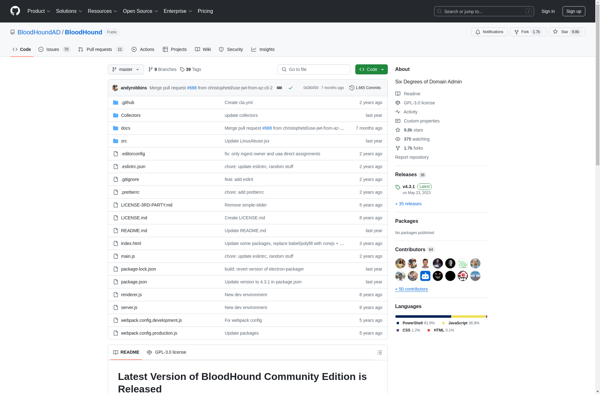
Description: BloodHound is an open source security tool used to analyze Active Directory environments and find relationships between different objects. It helps identify attack paths that could potentially allow an attacker to escalate privileges.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
Description: The Social-Engineer Toolkit is an open-source penetration testing framework designed for social engineering attacks. It includes a variety of custom attack vectors that enable red teams and security researchers to simulate phishing, vishing, SMSishing and USB autorun attacks.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API