Description: Stealthnet is a decentralized VPN service that provides anonymous network connections. It protects user privacy and provides secure internet access while masking your identity and browsing history.
Type: Open Source Test Automation Framework
Founded: 2011
Primary Use: Mobile app testing automation
Supported Platforms: iOS, Android, Windows
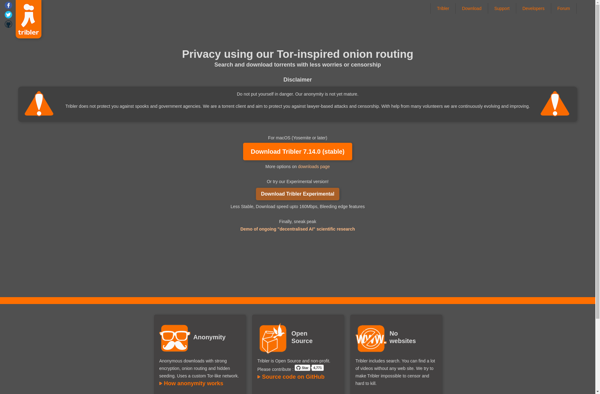
Description: Tribler is a decentralized BitTorrent client that allows anonymous peer-to-peer file sharing and video streaming without relying on centralized servers. It uses a robust incentive layer based on blockchain technology to reward users who contribute resources and seed content.
Type: Cloud-based Test Automation Platform
Founded: 2015
Primary Use: Web, mobile, and API testing
Supported Platforms: Web, iOS, Android, API