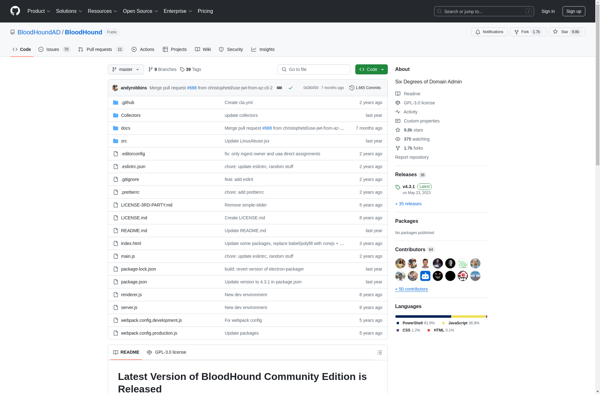
Description: BloodHound is an open source security tool used to analyze Active Directory environments and find relationships between different objects. It helps identify attack paths that could potentially allow an attacker to escalate privileges.
Type: software
Pricing: Open Source
Description: ZoomEye is a search engine and data mining tool for cyberspace that facilitates the discovery and analysis of devices exposed to the public internet. It allows users to search for open ports, identify software and their versions, and uncover security risks.
Type: software