Bokken
Bokken: Open-Source GUI for Pyew and Radare2 Reverse Engineering
Bokken allows users to disassemble, debug, and analyze malware without needing extensive knowledge of command line tools, aiming to be an intuitive and easy-to-use reverse engineering tool.
What is Bokken?
Bokken is a graphical user interface intended to be used with pyew and radare2 reverse engineering frameworks. It allows users to disassemble, debug, and analyze malware binaries without needing to have extensive knowledge of command line tools or reverse engineering concepts.
Some key features of Bokken include:
- Intuitive user interface for analyzing PE, ELF, and Mach-O binaries
- Integration with Pyew allows performing heuristic analysis of malware samples
- Integration with Radare2 allows disassembling and debugging binaries
- Advanced code analysis techniques such as control flow graphs and cross references
- Scriptable interface through Python plugins
- Supports analyzing Windows, Linux, OS X, and other platforms
The goal of the Bokken project is to lower the access threshold for analyzing and understanding malware through reverse engineering. It aims to put enterprise-level reverse engineering capabilities within reach of security professionals, malware analysts, forensic investigators, and hobbyists. Being open source allows the Bokken community to continually add features and analysis modules over time.
Bokken Features
Features
- Graphical user interface
- Integration with Pyew and Radare2
- Disassembly view
- Hexdump view
- Strings view
- Entropy view
- Function recognition
- Signature-based scanning
- Python scripting API
Pricing
- Open Source
Pros
Cons
Official Links
Reviews & Ratings
Login to ReviewThe Best Bokken Alternatives
View all Bokken alternatives with detailed comparison →
Top Security & Privacy and Reverse Engineering and other similar apps like Bokken
Here are some alternatives to Bokken:
Suggest an alternative ❐OllyDbg

ODA Online Disassembler
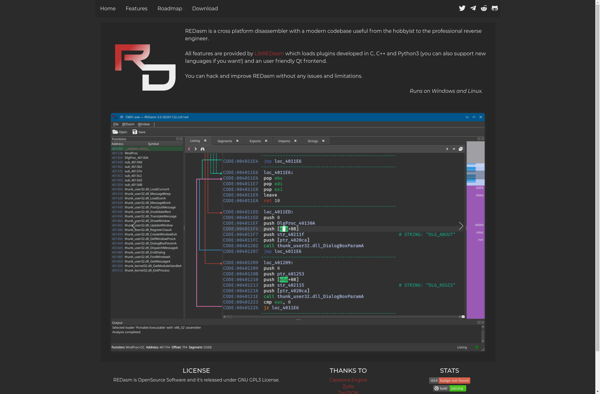
REDasm
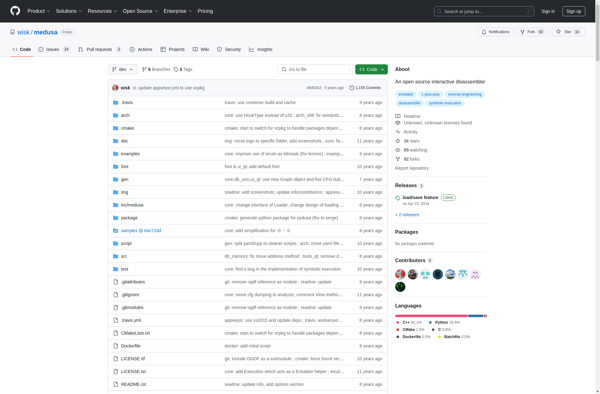
Medusa - Disassembler
Relyze