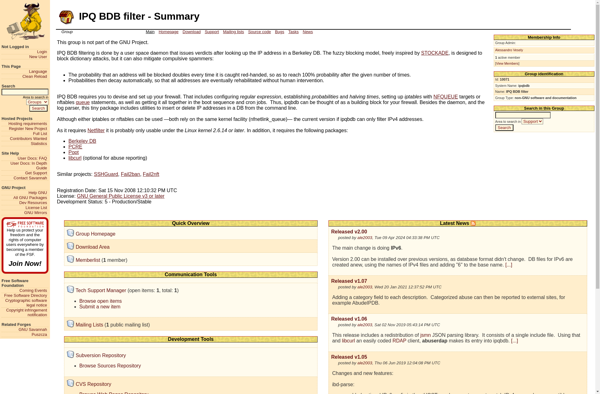
IPQ BDB
IPQ BDB is a database software designed for storing and managing large volumes of IP network traffic data. It allows efficient storage and analysis of network metadata.
IPQ BDB: Database Software for Managing Large Volumes of IP Network Traffic
Database software designed for storing and managing large volumes of IP network traffic data, allowing efficient storage and analysis of network metadata
What is IPQ BDB?
IPQ BDB is a high-performance database software optimized for storing and analyzing large volumes of IP network traffic data. It is designed to efficiently handle the storage and querying of massive amounts of network metadata.
Key features of IPQ BDB include:
- Specialized data structures for fast lookups and inserts of IP network data
- Scalable architecture that can handle billions of IP flows per day
- Advanced compression algorithms to minimize storage requirements
- Flexible schema that can accommodate new types of metadata
- SQL-based query interface for intuitive data analysis
- Indexing for fast searches by source, destination, time interval etc
- APIs for integration with other network tools and monitoring solutions
IPQ BDB allows network engineers and security analysts to store complete network histories for post-analysis. Its performance optimizations for network traffic metadata make it suitable for network forensics, security analytics, and compliance reporting.
IPQ BDB Features
Features
- Stores and manages large volumes of IP network traffic data
- Performs real-time analysis of network metadata
- Provides fast data ingestion and query performance
- Integrates easily with other network monitoring tools
- Offers flexible schema design for custom data models
- Scales horizontally to handle increasing data volumes
Pricing
- Subscription-Based
- Pay-As-You-Go
Pros
Handles large data volumes efficiently
Fast query response times
Flexible and customizable
Scales to meet growing needs
Integrates with existing systems
Purpose-built for network data analytics
Cons
Can require significant infrastructure resources
Limited ad-hoc query capabilities
Steep learning curve
Requires expertise to tune for performance
Not ideal for transactional workloads
Limited ecosystem of third-party tools
Reviews & Ratings
Login to ReviewThe Best IPQ BDB Alternatives
View all IPQ BDB alternatives with detailed comparison →
Top Network & Admin and Database Management and other similar apps like IPQ BDB
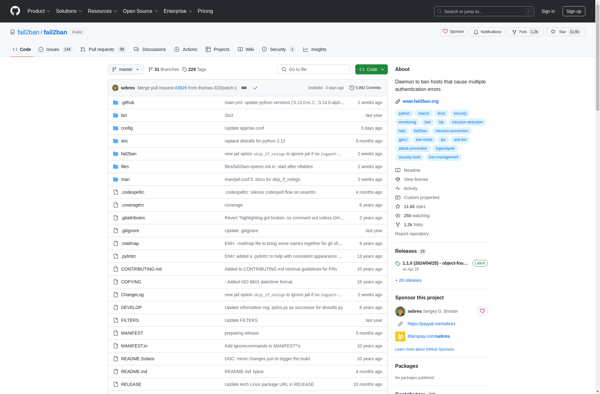
Fail2ban
Fail2ban is an open source intrusion prevention software framework designed to protect computer servers from brute-force attacks. It works by monitoring log files for signs of suspicious activity and banning IP addresses that attempt too many failed login attempts.Once Fail2ban detects multiple failed login attempts from the same IP address...
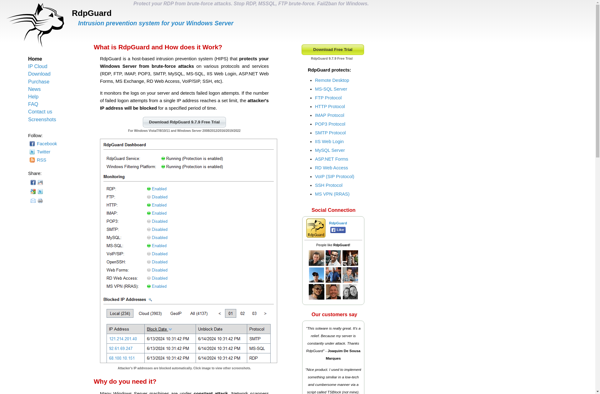
RdpGuard
RdpGuard is a software application designed specifically to protect Remote Desktop Protocol (RDP) connections against brute force cyber attacks. It works by monitoring all login attempts to RDP and employing various security measures to block attackers.Some of the key features of RdpGuard include:IP blacklisting - Automatically blacklist IP addresses after...
IPBanPro
IPBanPro is a powerful IP blocking and banning software used to protect websites by restricting access from unwanted or threatening visitors. It works by analyzing website traffic in real-time and using intelligent algorithms to detect suspicious and malicious activity.Once a potentially malicious IP address is identified, IPBanPro can automatically block...
AiP Defense
AiP Defense is an advanced cybersecurity software solution powered by artificial intelligence and machine learning. It provides real-time protection against a wide range of cyber threats including malware, ransomware, phishing attempts, unauthorized access, data exfiltration, and more.Unlike traditional antivirus software, AiP Defense does not rely on known threat signatures. Instead,...

Cyberarms Intrusion Detection and Defense
Cyberarms Intrusion Detection and Defense is a comprehensive network security software solution designed to monitor enterprise networks in real-time and detect malicious activity and cyberattacks. It works by analyzing traffic patterns and system behaviors to identify anomalies that could indicate a security breach or policy violation.The software uses a combination...
E.guardo Smart Defender
e.guardo Smart Defender is a comprehensive cybersecurity solution designed to safeguard devices and data against online threats like malware, ransomware, phishing scams, and hackers. It utilizes advanced AI and machine learning algorithms to provide real-time protection against even zero-day attacks.Key features of e.guardo Smart Defender include:Multi-layered threat prevention system including...
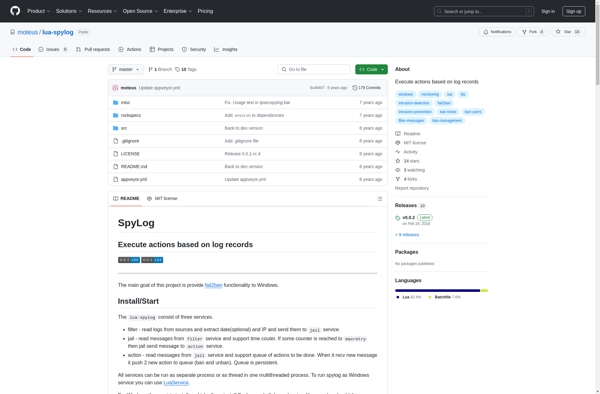
SpyLog
SpyLog is a powerful employee monitoring and activity tracking software used by companies to monitor their employee's activity on work computers. It provides a comprehensive set of features to track website visits, capture screenshots and keystrokes, log application and file usage, record chat and email communications, and monitor productivity.Some key...
Denyhosts
DenyHosts is an open-source program created in Python that helps system administrators prevent dictionary and brute force SSH attacks by analyzing SSH server log files to identify IP addresses that are performing multiple failed login attempts. When DenyHosts detects an IP address that has surpassed the allowed threshold for failed...
SSHGuard
SSHGuard is an open source intrusion prevention software designed to protect Linux and BSD based systems that run SSH servers. It analyzes system log files in real-time to detect attacks such as brute force attempts to guess passwords, scans searching for SSH server vulnerabilities, and other common attacks targeting systems...

Win2ban
Win2ban is an open source intrusion prevention software framework for Linux-based servers. It works by scanning log files for signs of abuse or malicious activity, and blocking repeat offenders via firewall rules.Some key features of win2ban include:Monitoring services such as SSH, Apache, Postfix, etc. for signs of brute force attacks,...